

Congratulations to Elmrep celebrating 40th anniversary!
Elmrep was founded in 1984 at Elm House, in a little village just outside of Gloucester, as a company supplying […]

Elmrep was founded in 1984 at Elm House, in a little village just outside of Gloucester, as a company supplying […]
Fantastic morning on our C2S Digital networking event! Great to see everyone for our award-winning digital networking event as always. […]

Minister for Manufacturing needed as nine in ten firms unhappy with government support for sector Audit, tax, advisory and risk […]
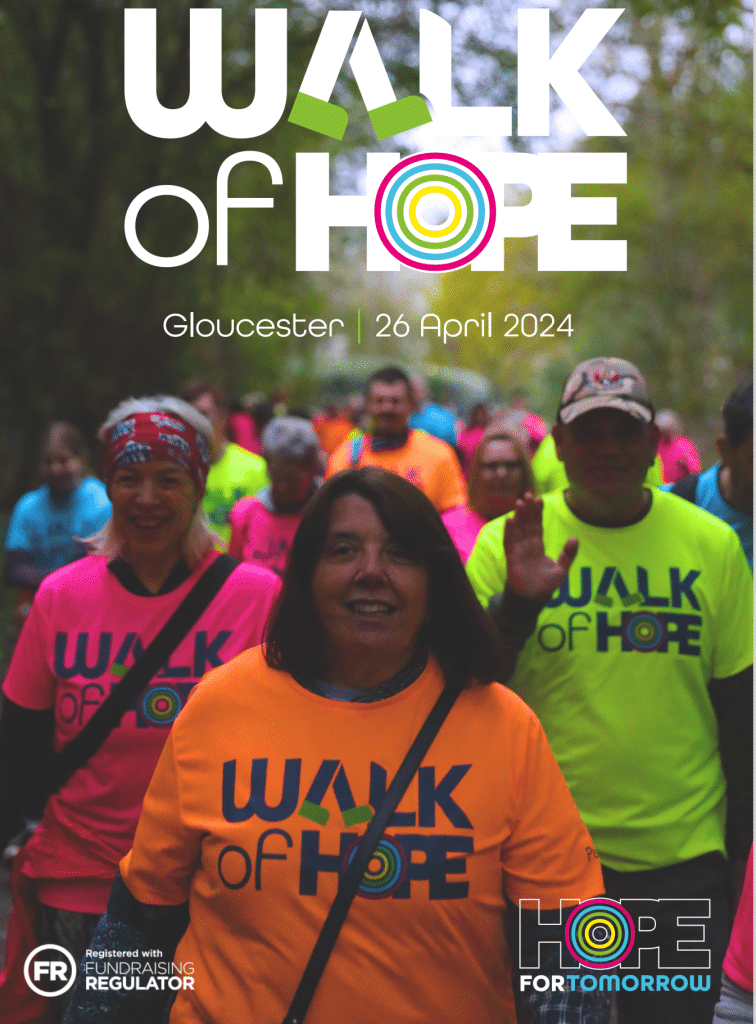
We’re bringing back the much-loved Walk of Hope, but this time in Gloucestershire! We’ll be taking to the streets of […]
Earlier this week we had the pleasure of Suzanne Hall-Gibbins from Circle2Success Ltd joining us in the Square One […]

Mental health issues can manifest in various ways, often subtle and easy to overlook. By being aware of the signs, […]

Boeing will now distribute about 1,000 additional actuation and propulsion system products. Boeing continues to expand its exclusive distributor partnership […]

C2S Business Awards 2024 What a Great Night Celebrating with Shortlisted Entrants, A Full House….. A look back at the […]

When & where Date: Wednesday 22/05/2024 Time: 5:00pm – 6:30pm At: BPE – St James House, Cheltenham, This FREE event is for non-members and […]

Join us for a relaxing evening, networking and catching up with other businesspeople in the beautiful bar at the iconic […]

Canny Conversations has merged with OPS-BOX to create Tandem Consultancy – a stronger combined business, enabling them to better serve […]

Friday 10th May 2024 Wine & Cheese Evening In partnership with Forest Deli, our beloved Cheese supplier, we will be […]

Apprenticeships are available across a very wide range of industry sectors and are an excellent way of gaining nationally recognised […]

A note from our Head of Global Intelligence, Gareth Westwood In what has been a tumultuous first quarter of 2024, […]

St Faith’s became a registered nursing home in March 1974 and the first nursing home for our charity Lilian Faithfull […]

Public Hearts Defibrillator Campaign CIC is immensely proud to install its 75TH defibrillator. With 6 going in pre-Covid and an […]

27 March 2024, Cheltenham, UK: Cheltenham-based technology and digital innovation provider, Emerge Digital has today announced a bumper round of new partnerships in the […]

University of Gloucestershire’s Ellie Sonmezer is preparing for a demanding six-day trek across parts of South East Asia in aid of […]

Good Energy has been announced as the official sponsor of The Festival of Sustainable Homes. The event, due to be […]

Ross Prince has been named as the new Office Managing Partner for national audit, tax, advisory and risk firm Crowe […]

Simplicity, a market-leading provider of recruitment funding and back-office solutions, proudly commemorates its 20th anniversary in business. Established in 2004 […]
Topics that are top of mind of C2S business people in 2024 Business people had a lot to navigate in […]

Linc Charity Polo Networking Day Friday 31st May 2024, 11.30am – 6pm We would love you to join us for […]

RE Recruitment, the award-winning agency in Cheltenham has acquired Truly Tailored Recruitment, a boutique recruitment agency known for its personal […]
